State of My Lab Q1 2026
Table of Contents
Two years ago I started my first Homelab. It was a Dell XPS laptop running a Minecraft server for me and my friends. Now it has grown into something much bigger, including enterprise-grade servers & networking equipment that I rely on every day.
1. Hardware#
| Name | Model | Location | RAM | CPU | Storage | Purpose |
|---|---|---|---|---|---|---|
| SW01 | Arista 7010T-48 | U13 | N/A | N/A | N/A | Core Switch |
| SW02 | Netgear GS105 | U13 | N/A | N/A | N/A | “WAN” Switch |
| SW03 | Netgear GS108 | U13 | N/A | N/A | N/A | OOBM Switch |
| PVE01 | HPE ProLiant DL360 Gen9 | U12 | 128GB | 2x Intel Xeon E5-2673 v3 | ~1.1 TB | PVE Node |
| PVE02 | HPE ProLiant DL360p Gen8 | U11 | 32GB | 2x Intel Xeon E5-2640 v1 | ~240 GB | PVE Node |
| PVE03 | HP EliteDesk 705 G4 | U15 | 48GB | AMD Ryzen 5 PRO 2400GE | ~1 TB | PVE Node |
| K3S04 | Raspberry Pi 5 | Top of rack | 8GB | N/A | 64 GB | Kube Node |
| K3S05 | Raspberry Pi 5 | Top of rack | 8GB | N/A | 64 GB | Kube Node |
| K3S06 | Raspberry Pi 5 | Top of rack | 8GB | N/A | 64 GB | Kube Node |
| NAS01 | N/A | Floor | 24GB | AMD FX-6100 | ~12 TB | NAS |
2. Networking#
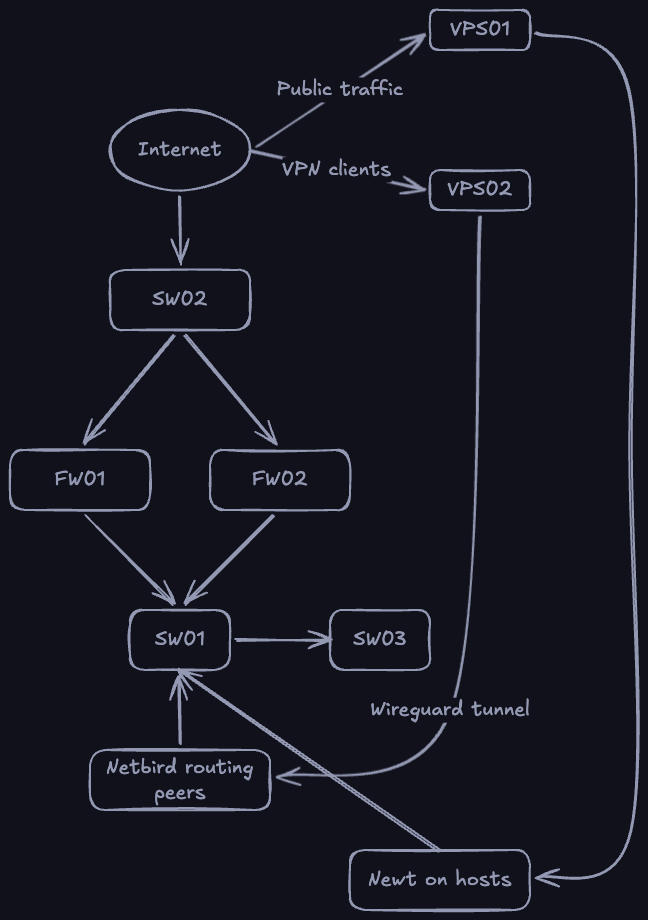
2.1. Topology#
2.2. Routing & Switching#
I currently run two instances of pfSense virtualized inside of proxmox which act as my gateways / routers / firewalls. I use my Arista 7010T (SW01) as my core switch, with a GS105 as my “WAN” switch and a GS108 as my OOBM switch.
What is the “WAN” switch?#
The WAN switch (SW02) is the switch that the WAN interfaces of both of my pfSense instances connect to. I place WAN in parentheses as it technically isn’t a WAN, just the LAN of the network provided by my ISP router
2.3. Segmentation#
My network currently consists of 6 VLANs
| Name | Tag | Purpose |
|---|---|---|
| LAN | 1 | Default network |
| DMZ | 78 | Segment publicly accessible services |
| Kube | 79 | Kubernetes cluster (K3sCl01) |
| Game | 80 | Wings deployments |
| Kube2 | 81 | Kubernetes cluster (K3sCl02) |
| OOBM | 82 | Management interfaces |
2.4. IP Ranges#
Time to mention my completely overkill IP Address allocations
I assign each VLAN its own /16 subnet from within 10.0.0.0/8 where the 2nd octet is the vlan tag. For example, DMZ has the subnet range 10.78.0.0/16. Inside each of these /16 subnets, I have 10.x.255.0/24 allocated for DHCP
The only exception to this rule is LAN, which has the subnet of 10.77.0.0/16.
2.5. DNS & DHCP#
I currently use the built-in “Kea DHCP” from pfSense for my DHCP and have no plans for changing within the near future.
For my DNS however, I currently run AdGuard Home, and am planning on switching to PowerDNS as it is more enterprise grade and seems like a fun project to work on.
3. Compute#
For compute, I currently have a proxmox cluster which runs a majority of my workload and two kubernetes clusters, one of which is for hosting external services, such as this website.
3.1. Proxmox Cluster#
My proxmox cluster consists of 3 nodes, one of which is a HP mini pc which I hope to replace with another DL360 G8/9 within the near future.
Every major VM creates a backup at midnight every night to NAS01 over NFS.
3.2. Kubernetes Clusters#
I run two Kubernetes clusters in my lab, one for internal services (K3sCl01), and one for external services (K3sCl02). I did this to mimic my setup in proxmox where I have local services on my LAN VLAN, and public services on my DMZ. But instead I chose to put each cluster on its own VLAN, which gives me more control over what each cluster is permitted to access.
4. Storage#
4.1. NAS01#
NAS01 is currently my one and only NAS, It is where I store all my media & backups, however I do have plans to replace this machine soon.
NAS01 is an old desktop PC that I put 4x 3TB NAS drives in running a RAIDZ1 ZFS pool. It is running TrueNAS and has been perfect for me so far, however I would like to switch to something with more drive bays, and something I can properly mount in the rack.
4.2. Backblaze#
I currently have an account with Backblaze with nothing stored. However I plan to have an off-site backup of NAS01, and to store my terraform state with them.
5. Services & Systems#
5.1. Storage#
- TrueNAS
- Backblaze
- Longhorn
- Postgres
5.2. Infrastructure#
- Proxmox VE
- Kubernetes
- Docker
- Helm
5.3. Networking#
- pfSense
- Cloudflare
- Traefik
- Pangolin
- AdGuard Home
- Gluetun
- MetalLB
- Middleware Manager
- Netbird
- Proton VPN
- Tailscale
5.4. Media#
- Jellyfin
- Radarr
- Sonarr
- Prowlarr
- qBittorrent
5.5. Communication#
- Matrix Synapse
- Proton Mail
5.6. Management#
- iLO
5.7. Security#
- Authentik
- HashiCorp Vault
- Cert Manager
- External Secrets Operator
5.8. Monitoring#
- Grafana
- Prometheus
- Loki
- Alloy
- Checkmk
5.9. AI#
- n8n
5.10. Gaming#
- Pterodactyl Panel
- Wings
5.11. Automation#
- Terraform
- Ansible
5.12. CI/CD#
- GitLab
6. What’s Next?#
In Q2 I plan to buy another DL360 to replace the mini pc that has been with me for around 1.5 years and have my proxmox cluster be fully enterprise. I also hope to replace my NAS, purchase a UPS, Deploy Vaultwarden, ArgoCD, and migrate to PowerDNS.
Thanks for reading :)